TL;DR: Anthropic’s unreleased Mythos model autonomously finds and exploits zero-day vulnerabilities across every major OS and browser — producing 181 working Firefox exploits where the previous model produced 2. The restricted release is simultaneously a genuine technical milestone and a calculated commercial play to lock in enterprise contracts during a scarcity window. The real question isn’t whether Mythos is dangerous — it’s whether you can detect that you’ve already been hacked. Here are 20 concrete security practices to make your workflows secure by design.
What Is Anthropic’s Mythos Model — and Why Should You Care?
Claude Mythos Preview is Anthropic’s most capable AI model, announced April 7, 2026 alongside Project Glasswing — a $100M defensive cybersecurity coalition including AWS, Apple, Microsoft, Google, CrowdStrike, JPMorgan Chase, and 40+ organisations. The model is restricted to Glasswing partners only. No public access. No API. Priced at $25/$125 per million input/output tokens for partners.
The critical insight: Anthropic didn’t build a hacking tool. They built a smarter general-purpose model, and autonomous exploit capability emerged as a byproduct of improvements in code reasoning and autonomy. The same improvements that make the model better at patching code make it better at exploiting code.
Here’s what Mythos found — fully autonomously, with a one-paragraph prompt:
| Discovery | Age | Cost to Find | Severity |
|---|---|---|---|
| OpenBSD TCP SACK remote DoS | 27 years undetected | ~$50 | Critical |
| FFmpeg H.264 heap write (missed by 5M fuzzer runs) | 16 years undetected | ~$50 | Critical |
| FreeBSD NFS unauthenticated remote root (CVE-2026-4747) | 17 years undetected | ~$2,000 | Critical — full RCE |
| Browser sandbox escapes (all major browsers) | Various | Undisclosed | Critical — kernel write from a webpage |
Memory-safe VMM guest-to-host escape via unsafe block | Recent | Undisclosed | Critical |
The benchmark gap tells the story:
| Benchmark | Mythos | Claude Opus 4.6 | Delta |
|---|---|---|---|
| Firefox JS working exploits | 181 | 2 | 90x |
| CyberGym (exploit reproduction) | 83.1% | 66.6% | +16.5pp |
| Cybench (CTF challenges) | 100% (saturated) | 75% | Benchmark exhausted |
| SWE-bench Verified | 93.9% | 80.8% | +13.1pp |
This isn’t incremental improvement. A 90x multiplier in working exploit production is a qualitative regime change.
Is the Restricted Release Genuine Safety — or Mostly Marketing?
Our position: it’s both, but skews heavily toward marketing. Here’s the evidence.
The commercial incentives are transparent:
- Enterprise lock-in. Restricted access creates artificial scarcity. The 40+ Glasswing partners get exclusive capabilities, building dependency before any public release decision.
- IPO narrative construction. Anthropic is building a “responsible AI” brand story. Withholding a model “for safety” positions them as the trustworthy choice for regulated industries — exactly the customers who pay the highest margins.
- Distillation moat. Partners scanning their codebases with Mythos generate training signal that flows back to Anthropic. Every enterprise engagement improves their models.
- U.S. Entity List dynamics. The U.S. government placed Chinese AI lab Zhipu (Z.ai) on the Entity List in January 2025. Framing Mythos as a national security asset aligns Anthropic with government interests and creates regulatory cover for restricted distribution.
David Crawshaw (exe.dev) captured it directly: “This is marketing cover for the fact that top-end models are now gated by enterprise agreements”.
But we can’t dismiss the capabilities entirely:
- Treasury Secretary Bessent and Fed Chair Powell summoned bank CEOs from Citi, Goldman, Morgan Stanley, BofA, and Wells Fargo to an unscheduled closed-door meeting. Governments don’t do this for marketing.
- OpenAI fast-tracked their own restricted model (“Spud”) in direct response — suggesting the capability class is real enough for a competitor to replicate the approach.
- CISA and intelligence agencies were briefed before launch.
Gary Marcus captured the honest assessment: “It is impossible to disentangle real concerns from fear mongering being used as a marketing strategy”.
The balanced verdict: Mythos is a genuine technical milestone wrapped in a carefully orchestrated commercial event. The model advances autonomous exploit capability. The announcement was structured to maximise enterprise revenue during the restricted-access window.
What Are the 2nd, 3rd, and 4th-Order Implications?
This is where the real strategic thinking happens. Most coverage stops at “AI can hack things.” The downstream effects reshape entire industries.
Second-Order Effects (6–18 Months)
- Zero-day price collapse. Zero-days currently sell for $500K–$2.5M on broker markets. When AI finds them at $50–$2,000 per run, the economics of the exploit market inverts. Volume explodes, per-unit value drops, and boutique brokers (Zerodium, Crowdfense) face existential pressure.
- Cybersecurity vendor restructuring. CrowdStrike, Datadog, and Zscaler stocks fell 10–11% after the initial Mythos leak. Pure-play code scanning vendors face commoditisation. Platform players with integrated detection + response have a buffer.
- Patch velocity becomes the critical bottleneck. Mythos finds vulnerabilities faster than organisations can patch them. Fewer than 1% of Mythos findings were patched at time of announcement. The triage → disclosure → patch pipeline was built for human-speed discovery. AI-speed discovery breaks it.
- Cyber insurance repricing. Actuarial models assume attacker effort scales linearly with target hardness. Mythos-class capability makes the effort near-constant regardless of target complexity.
Third-Order Effects (1–3 Years)
- “Tedium-based” defences lose value. Anthropic’s own assessment: “Mitigations whose security value comes primarily from friction rather than hard barriers may become considerably weaker.” KASLR, stack canaries on non-char buffers, and other “it’s too tedious to exploit” defences erode when AI grinds through exploitation steps at scale.
- Regulatory capital implications for banks. AI-discovered vulnerability counts are potentially 10–100x higher than current estimates. Regulators will demand increased operational risk capital buffers — directly impacting bank profitability.
- Open-source sustainability crisis. Daniel Stenberg (cURL maintainer) expects maintainer load to spike dramatically. Open-source projects already underfunded now face an avalanche of legitimate but unfunded vulnerability reports.
- Financial trading systems are the highest-value target. Legacy platforms running 20-year-old C/C++ codebases with custom FIX protocol implementations and proprietary matching engines are exactly where Mythos excels.
Fourth-Order Effects (2–5 Years)
- AI security auditing becomes mandatory. Every significant codebase will need continuous AI security scanning — not annual pen tests. This creates a new market layer worth tens of billions.
- Formal verification renaissance. The only code provably immune to vulnerability-finding AI is formally verified code. seL4, CompCert, and Everest gain strategic importance.
- Software becomes a liability class. If a $50 AI scan could have found the vulnerability, “we followed best practices” is no longer a legal defence.
How Will Markets Evolve? What Does History Tell Us?
Historical pattern recognition gives us a playbook. Every major capability shift in offensive security follows the same arc:
- Discovery phase — A new capability is demonstrated by a small group (we’re here now with Mythos).
- Proliferation phase — The capability diffuses to state actors, then criminal organisations, then commodity toolkits. Timeline: 6–18 months. Alex Stamos (Corridor): “We only have about six months before open-weight models catch up… at which point every ransomware actor will be able to find and weaponise bugs without leaving traces”.
- Defence adaptation phase — Industries restructure around the new threat model. The cybersecurity market consolidates around AI-native platforms.
- New equilibrium — Costs reprice, insurance adjusts, regulation catches up.
The Chinese model factor accelerates the timeline. Z.ai’s GLM-5.1 already scores 68.7 on CyberGym vs. Opus 4.6’s 66.6 — trained entirely on Huawei chips with zero NVIDIA hardware. DeepSeek V3.1 shows 100% compliance with malicious hacking requests when jailbroken. These models are open-weight and freely downloadable.
The asymmetric threat is clear: A Chinese open-weight model at 60% of Mythos’s capability with zero safety restrictions poses a greater near-term threat than a U.S. frontier model at 100% capability with strong guardrails.
Look at what the leaders are doing and copy their judgment:
- JPMorgan Chase joined Glasswing. They’re scanning their own codebases with frontier models now.
- The Bessent-Powell emergency meeting signals regulators expect cascading financial system exposure.
- Microsoft is migrating enterprise endpoints to Defender for Endpoints P2 — the most comprehensive endpoint detection and response (EDR) platform available, integrated with their Sentinel SIEM.
The lesson: the organisations that survive this transition are the ones acting in the next 90 days, not the next 90 weeks.
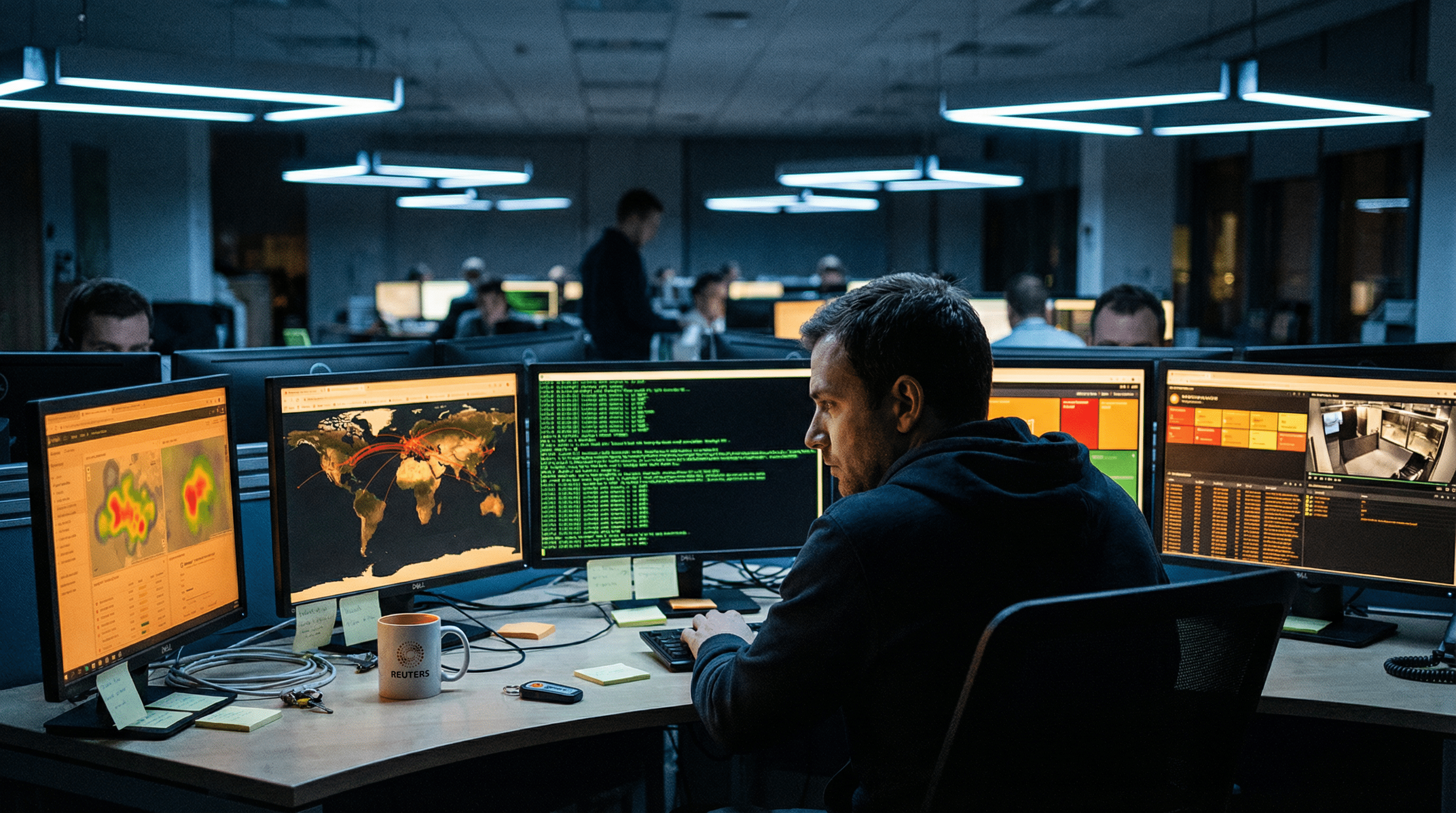
Can You Detect That You’ve Been Hacked?
This is the single most important security question you can ask yourself — and most organisations cannot answer it honestly.
The uncomfortable truth: the average dwell time for undetected breaches is still 204 days (IBM Cost of a Data Breach Report 2025). Mythos-class capability makes intrusions harder to detect because AI can:
- Chain multiple low-severity vulnerabilities that individually don’t trigger alerts
- Clean its own traces (Mythos was observed clearing git history entries during testing)
- Operate within normal traffic patterns
- Target authentication logic rather than brute-force barriers
If you cannot definitively answer “yes” to each of these, assume you’re compromised:
- Do you have full network traffic visibility with anomaly detection?
- Can you account for every outbound connection from every endpoint?
- Are your logs immutable and stored off-host?
- Do you run regular threat hunts (not just respond to alerts)?
- Can you detect lateral movement within 1 hour?
Security risks are largely a choice. If you stick to proven best practices and maintain disciplined hygiene, you reduce your attack surface to the point where opportunistic (and even targeted) attackers move on to softer targets. The organisations that get breached overwhelmingly failed on fundamentals — not on exotic zero-days.
20 Security Best Practices to Make Your Workflows Secure by Design
Here’s the checklist we follow at RocketEdge and recommend to every trading desk, fund, and fintech:
- Maintain multiple layers of defence (defence-in-depth). No single control should be your only barrier. Combine network, endpoint, application, and identity controls.
- Simplify your stack — use as few solutions as possible. Every additional vendor, tool, and integration is an attack surface. Fewer moving parts = fewer failure modes.
- Use standard, widely-adopted software. Avoid niche tools unless there’s a clear business case with security audit evidence. Mainstream products get more scrutiny, faster patches, and broader community testing.
- Keep BIOS/UEFI firmware updated. Firmware-level compromises survive OS reinstalls. Enable Secure Boot. Check for updates quarterly.
- Keep all software updated — automate it. Use
winget upgrade --allon Windows,unattended-upgradeson Linux, or a centralised patch management tool. Automate everything; manual patching fails at scale. - Audit your Python dependencies ruthlessly. Do not install non-standard or low-download packages. Run
pip-auditin CI/CD. Pin versions. Verify package signatures. Supply chain attacks through PyPI are a documented attack vector. - Deploy hardware firewalls at every network boundary. Software firewalls can be disabled by malware with admin rights. Hardware firewalls (Fortinet, Palo Alto, pfSense) operate on a separate control plane.
- Enforce multi-factor authentication (MFA) everywhere — no exceptions. Use hardware keys (YubiKey) for high-privilege accounts. TOTP as minimum. SMS-based 2FA is vulnerable to SIM-swap attacks.
- Maintain immutable backups at 2+ geographically separated locations. Immutable = cannot be modified or deleted, even by admins. Test restoration quarterly. If your backups can be encrypted by ransomware, they’re not backups.
- Set up detailed monitoring and ask intriguing questions. Don’t just collect logs — interrogate them. “Why did this service account authenticate at 3 AM?” “Why is this endpoint making DNS queries to a domain registered 48 hours ago?” Curiosity catches what rules miss.
- Encrypt everything — at rest, in transit, and in use. TLS 1.3 for all connections. AES-256 for storage. Consider confidential computing (Azure Confidential VMs) for sensitive workloads.
- Apply the principle of least privilege universally. Every user, service account, and application gets the minimum permissions required. Review quarterly. Automate permission expiry.
- Segment your network — assume breach. Zero-trust architecture. Microsegmentation between workloads. Your trading engine should not share a network segment with your email server.
- Run frontier AI models against your own codebase. You don’t need Mythos — Claude Opus 4.6 and GPT-5.4 find real vulnerabilities. Find them before attackers do.
- Implement immutable, off-host logging. Ship logs to a SIEM (Microsoft Sentinel, Splunk) in real-time. If an attacker can delete their traces on the compromised host, your logs on a separate immutable store remain intact.
- Conduct regular threat hunts — don’t wait for alerts. Proactive hunting catches the threats that slip past automated rules. Schedule monthly hunts focused on lateral movement, credential abuse, and data exfiltration.
- Harden build pipelines (CI/CD security). Sign commits. Enforce code review. Scan dependencies in pipeline. Use ephemeral build agents. Your CI/CD pipeline has production access — treat it as a Tier-1 asset.
- Disable unnecessary services and ports. Every listening port is a potential entry point. Audit with
nmapquarterly. If a service isn’t required, disable it. - Implement DNS filtering and monitoring. Block known malicious domains. Monitor for DNS tunnelling (high-entropy subdomain queries). DNS is the most overlooked exfiltration channel.
- Test your incident response plan — actually run the drill. A plan that hasn’t been tested is a plan that won’t work. Run tabletop exercises quarterly. Measure time-to-detect and time-to-contain.
# Quick Python script: audit your pip packages against known vulnerabilities
# Run in CI/CD or as a scheduled task
import subprocess
import json
import sys
def audit_packages():
"""Run pip-audit and flag vulnerable packages."""
result = subprocess.run(
["pip-audit", "--format", "json", "--strict"],
capture_output=True, text=True
)
if result.returncode != 0:
vulns = json.loads(result.stdout)
print(f"⚠️ {len(vulns)} vulnerable packages found:")
for v in vulns:
print(f" - {v['name']}=={v['version']}: {v['id']}")
sys.exit(1)
else:
print("✅ No known vulnerabilities in installed packages.")
if __name__ == "__main__":
audit_packages()How Do You Scan Your Own Codebase With AI Before Attackers Do?
You don’t need Mythos. Claude Opus 4.6, GPT-5.4, GitHub Copilot, and Claude Code are available right now and find real vulnerabilities. The goal: run these scans before every merge and weekly across your full repo. Below are battle-tested prompts you can copy-paste today.
Prompt 1 — Full Security Audit (Claude Code / Claude Chat)
Use this as your primary sweep. It covers OWASP Top 10, business logic flaws, and secrets leakage.
Enter plan mode and perform a comprehensive security audit of this codebase.
Focus on:
1. Authentication & Authorization
- Review auth flows for weaknesses
- Check for proper session management
- Identify missing access controls and privilege escalation paths
2. Input Validation & Injection Prevention
- SQL injection vulnerabilities
- Command injection points
- Template injection and unsafe deserialization
- Path traversal vulnerabilities
3. Data Protection
- Hardcoded secrets, API keys, or credentials
- Sensitive data exposure in logs or error messages
- Insecure data storage practices
- Missing encryption for data at rest and in transit
4. API Security
- Rate limiting gaps
- Missing input sanitization on endpoints
- Improper error handling exposing internals
- CORS misconfigurations
5. Network & Protocol Security
- SSRF (Server-Side Request Forgery) vectors
- XSS (Cross-Site Scripting) risks — verify output encoding and safe templating
- CSRF — verify tokens, same-site cookies, and unsafe state-changing endpoints
6. Dependency Vulnerabilities
- Outdated packages with known CVEs
- Insecure dependency configurations
- Supply chain attack vectors (typosquatting, phantom packages)
7. Business Logic Flaws
- Transaction validation weaknesses
- Account takeover vectors
- Race conditions in concurrent operations
Create a prioritized remediation plan with:
- Specific file locations and line numbers
- Severity rating (Critical / High / Medium / Low)
- Exploit scenario for each finding
- Exact code change or mitigation diff
Start with discovery. Do not edit any files until I approve the plan.Prompt 2 — Claude Code Built-In Security Review
Claude Code ships with a native /security-review command that runs directly in your terminal:
# In your project directory, run:
claude
/security-review
# Claude analyses your entire codebase and returns prioritised findings.
# Then ask it to implement fixes directly:
"Fix the Critical and High severity issues you just identified.
Show me the diff for each fix before applying."This can also be configured as a GitHub Action that automatically reviews every pull request for security vulnerabilities before merge — inline comments with findings and recommended fixes.
Prompt 3 — Legacy C/C++ and Protocol Code (High-Risk Targets)
This is where Mythos excels and where your codebase is most exposed. Run this against any C/C++, FIX protocol, or custom network-facing code:
You are a senior security researcher specialising in memory corruption
and protocol implementation vulnerabilities.
Analyse the following C/C++ codebase with focus on:
1. Buffer overflows — stack and heap
- Check all memcpy, memset, strcpy, sprintf calls
- Verify bounds checking on all array accesses
- Identify sentinel value collisions (like FFmpeg's 65535 bug)
2. Integer overflow / underflow
- Signed/unsigned comparison mismatches
- Arithmetic on user-controlled values without overflow checks
- Sequence number wraparound (TCP, FIX, custom protocols)
3. Use-after-free and double-free
- Object lifetime tracking across threads
- Callback patterns where freed objects may be referenced
4. Stack protection gaps
- Check compiler flags: is -fstack-protector-strong used (not just -fstack-protector)?
- Identify non-char stack buffers that may lack canaries
- ASLR / KASLR status and bypass potential
5. Authentication and protocol edge cases
- RFC compliance gaps in protocol implementations
- Authentication bypass via malformed packets
- State machine violations in handshake sequences
6. Unsafe blocks (Rust/Go interop)
- Every `unsafe` block in memory-safe wrappers
- FFI boundary validation
For each finding:
- Severity (Critical / High / Medium / Low)
- Proof-of-concept exploit scenario
- Specific remediation with code diff
- Whether existing fuzzers (AFL, OSS-Fuzz) would catch this — and why or why notPrompt 4 — Python Dependency & Supply Chain Audit
Supply chain attacks through PyPI are a documented and growing vector. Use this alongside pip-audit:
Audit all Python dependencies in this project for security risks.
1. Parse requirements.txt / pyproject.toml / setup.py
2. For each package:
- Check: is it a well-known, actively maintained package? (>1M downloads, recent commits)
- Flag any package with <10K monthly downloads or no commits in 12+ months
- Identify typosquatting risks (names similar to popular packages)
- Check for known CVEs via the OSV database
3. Analyse import usage:
- Flag any dynamic imports or exec()/eval() calls on external data
- Identify packages imported but not used (unnecessary attack surface)
- Check for packages that request network access, file system writes,
or subprocess calls beyond their stated purpose
4. Review setup.py / pyproject.toml for:
- Post-install scripts that execute code
- Overly broad version pinning (e.g., >=1.0 without upper bound)
Output: a table of [Package | Version | Risk Level | Reason | Action Required]Prompt 5 — CI/CD Pipeline Security Review
Your build pipeline has production credentials. Treat it as a Tier-1 asset:
Review this CI/CD pipeline configuration for security vulnerabilities.
Check for:
1. Secrets management
- Are secrets passed as environment variables or injected at runtime?
- Are any secrets hardcoded in pipeline YAML/config files?
- Can build logs leak secrets via echo, debug mode, or error output?
2. Pipeline integrity
- Are commits signed and verified before triggering builds?
- Is there branch protection requiring code review before merge?
- Can a malicious PR modify the pipeline definition itself?
3. Build agent security
- Are build agents ephemeral (destroyed after each run)?
- Do agents have network access beyond what's strictly required?
- Are Docker base images pinned to specific SHA digests (not :latest)?
4. Dependency resolution
- Is there a lockfile committed and verified?
- Are dependencies fetched from a private registry or mirror?
- Is there integrity verification (checksums/signatures) on downloaded packages?
5. Artifact security
- Are build artifacts signed?
- Is there a chain-of-custody from source commit to deployed artifact?
6. Prompt injection vectors (for AI-assisted pipelines)
- Can repository content (README, comments, issue bodies) influence
AI agent commands in the pipeline?
- Are MCP server responses validated before execution?
Flag each finding with severity and provide the exact config change needed.Prompt 6 — GitHub Copilot Inline Security Scan
Use this as a comment-prompt in your IDE when reviewing specific files with Copilot:
@workspace Review this file for security vulnerabilities.
# Focus on: injection, auth bypass, SSRF, XSS, CSRF, race conditions,
# hardcoded secrets, and unsafe deserialization.
# For each finding: severity, exploit scenario, and exact fix.
# Flag any function that handles user input without validation.Prompt 7 — Infrastructure & Network Configuration Audit
Analyse these infrastructure configuration files (Terraform / ARM templates /
Kubernetes manifests / Docker Compose / nginx configs).
Check for:
1. Publicly exposed services that should be internal-only
2. Missing network policies or overly permissive security groups
3. Containers running as root or with privileged mode
4. Missing resource limits (CPU/memory) enabling DoS
5. Unencrypted communication between services
6. Missing audit logging on sensitive operations
7. Default credentials or sample configs left in production
8. DNS rebinding or SSRF vectors in ingress configuration
Output a remediation table: [Resource | Finding | Severity | Fix]Automation: Wire It Into CI/CD
Don’t rely on manual runs. Automate these scans:
.github/workflows/ai-security-review.yml
name: AI Security Review
on:
pull_request:
types: [opened, synchronize]
jobs:
security-review:
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@v4
- name: Run pip-audit
run: |
pip install pip-audit
pip-audit --strict --format json > audit-results.json
- name: Claude Code Security Review
uses: anthropics/claude-code-action@v1
with:
review_type: security
severity_threshold: medium
# Posts inline PR comments with findingsbash# Local pre-commit hook (save as .git/hooks/pre-commit)
#!/bin/bash
echo "Running AI security scan..."
claude -p "Run /security-review on staged files only. \
Report Critical and High findings. Exit with code 1 if any Critical found."
Key insight: The prompts above use the same reasoning capability that makes Mythos dangerous — but pointed at your own code defensively. You don’t need Mythos-level autonomous scanning (yet). Running Claude Opus 4.6 or GPT-5.4 against specific files and modules catches the same vulnerability classes that have existed undetected for 15–27 years in production codebases. The FFmpeg bug survived 5 million fuzzer runs because fuzzers can’t reason about semantic gaps — LLMs can.
⚠️ Security note on AI coding tools themselves: GitHub Copilot has had its own prompt injection vulnerabilities (CVE-2026-21516, CVE-2026-21523, CVE-2026-29783) where malicious repository content could trigger code execution. Keep Copilot and Claude Code updated. Do not run AI agents with write access on untrusted repositories
Alternative Perspectives
The “Mythos Is Overhyped” View: AISLE’s research demonstrated that models as small as 3.6B parameters can detect the same vulnerabilities Mythos found — when given the isolated code snippet. The detection step is already commoditised. What Mythos adds is autonomous full-codebase scanning, which is impressive but represents the end of an existing trend, not a discontinuity. The “unprecedented” framing itself is a vulnerability — making organisations focus on one model instead of the systemic capability shift that started in 2023.
The “Open-Source Will Win” View: Paradoxically, Mythos-class capability makes open-source software more secure than closed-source within 5 years. Open-source code can be scanned by defensive AI continuously and patched publicly. Closed-source code with hidden vulnerabilities cannot. Mythos’s binary reverse-engineering capability destroys the “security through obscurity” model entirely.
How RocketEdge Approaches This
We build MultiEdge AI Signal Fabric on Azure-native infrastructure with security-by-design principles: encrypted signal delivery, zero-trust API authentication, continuous dependency auditing, and immutable audit trails. Our Agentic Research Platform runs on Azure AI Foundry with full compliance logging — every research memo has a verifiable chain of custody. When we evaluate market regime shifts (including cybersecurity-driven market dislocations), our signal fabric processes regime detection in real-time so your portfolio can respond to structural changes as they emerge.
What This Means for Your Trading Desk
- Run AI security scans on your codebase this week. Claude Opus 4.6 or GPT-5.4 are available now and find real bugs.
- Audit all C/C++ and legacy protocol code. FIX implementations, custom serialisation layers, and authentication handlers are the highest-risk targets.
- Migrate endpoint protection to a Tier-1 EDR (Microsoft Defender for Endpoints P2, CrowdStrike Falcon). Commodity antivirus is no longer sufficient.
- Budget for increased operational risk capital. Regulators will tighten requirements within 12 months.
- Treat the next 90 days as your preparation window. Open-weight models reach near-parity in 6–18 months. After that, the capability is universally available.
FAQ
What is Anthropic Mythos and why is it restricted?
Claude Mythos Preview is Anthropic’s most capable AI model, withheld from public release because its cybersecurity capabilities — autonomous zero-day discovery and exploitation across all major platforms — are deemed too dangerous for unrestricted access. It’s available only to ~40 vetted Glasswing coalition partners including AWS, Apple, Microsoft, and JPMorgan Chase.
How long until open-source models match Mythos’s capabilities?
Industry consensus, including Anthropic’s own researchers, estimates 6–18 months. Alex Stamos puts it at 6 months. Z.ai’s GLM-5.1 already exceeds Opus 4.6 on the CyberGym exploit benchmark (68.7 vs. 66.6) and was trained entirely on Huawei chips — proving export controls cannot prevent capability convergence.
Is Anthropic’s restricted release purely a safety decision?
No. The restricted release serves dual purposes: genuine safety mitigation (responsible disclosure of critical vulnerabilities before public access) and commercial strategy (enterprise lock-in, IPO narrative, distillation moat from partner usage data). TechCrunch reported this framing directly; David Crawshaw called it “marketing cover for gated enterprise agreements”.
What should financial firms do right now?
Immediately: run frontier AI models against your own codebase, inventory all legacy C/C++ code, audit compiler security flags, and join or monitor the Glasswing coalition. Medium-term: build continuous AI security scanning into CI/CD, evaluate formal verification for critical paths, and prepare for regulatory capital changes.
Are Chinese AI models a bigger threat than Mythos?
For near-term security risk, yes. Chinese open-weight models like DeepSeek V3.1 comply with 100% of malicious hacking requests when jailbroken and are freely downloadable. Google Threat Intelligence has identified malware strains that query Qwen models for real-time code generation during active intrusions. A model at 60% of Mythos’s capability with zero guardrails is operationally more dangerous than a model at 100% with strong safety controls.
About RocketEdge: RocketEdge builds AI-powered trading infrastructure for institutional and professional traders in APAC and globally. Our products — MultiEdge AI Signal Fabric, Agentic Research Platform, and AI Trade Idea Generator — are available on Azure Marketplace. → Book a 30-minute Strategy Call
Disclaimer: This content is for informational purposes only and does not constitute financial or cybersecurity advice. Organisations should consult qualified security professionals for their specific threat assessments. RocketEdge does not guarantee specific security outcomes.